‘Sigma Rules List’ PDF Quick download link is given at the bottom of this article. You can see the PDF demo, size of the PDF, page numbers, and direct download Free PDF of ‘Sigma Rules List with Examples’ using the download button.
Sigma Rules List with Examples Book PDF Free Download
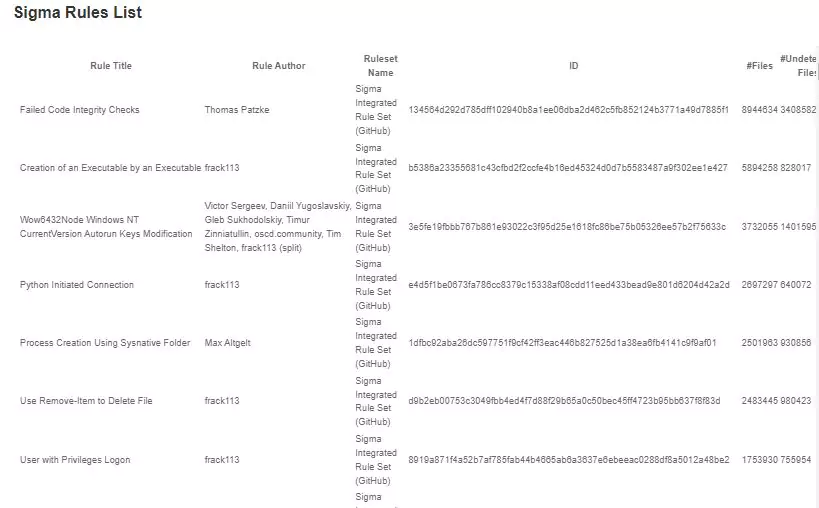
Sigma Rules List
| Rule Title | Rule Author | Ruleset Name | Files | Undetected Files |
|---|---|---|---|---|
| Autorun Keys Modification | Victor Sergeev, Daniil Yugoslavskiy, Gleb Sukhodolskiy, Timur Zinniatullin, oscd.community, Tim Shelton | Sigma Integrated Rule Set (GitHub) | 21401557 | 53952 |
| Suspicious Run Key from Download | Florian Roth | Sigma Integrated Rule Set (GitHub) | 8252741 | 5330 |
| Stop Windows Service | Jakob Weinzettl, oscd.community | Sigma Integrated Rule Set (GitHub) | 6831397 | 38789 |
| Net.exe Execution | Michael Haag, Mark Woan (improvements), James Pemberton / @4A616D6573 / oscd.community (improvements) | Sigma Integrated Rule Set (GitHub) | 6451515 | 35190 |
| Milum malware detection (WildPressure APT) | Ariel Millahuel | SOC Prime Threat Detection Marketplace | 6291968 | 24 |
| Non Interactive PowerShell | Roberto Rodriguez @Cyb3rWard0g (rule), oscd.community (improvements) | Sigma Integrated Rule Set (GitHub) | 3991193 | 105250 |
| Always Install Elevated Windows Installer | Teymur Kheirkhabarov (idea), Mangatas Tondang (rule), oscd.community | Sigma Integrated Rule Set (GitHub) | 3025326 | 55602 |
| File Created with System Process Name | Sander Wiebing | Sigma Integrated Rule Set (GitHub) | 2284944 | 13926 |
| Windows Processes Suspicious Parent Directory | vburov | Sigma Integrated Rule Set (GitHub) | 1851752 | 92 |
| Shade Ransomware (Sysmon detection) | Ariel Millahuel | SOC Prime Threat Detection Marketplace | 1673840 | 16 |
| Suspicious desktop.ini Action | Maxime Thiebaut (@0xThiebaut) | Sigma Integrated Rule Set (GitHub) | 1397422 | 161 |
| System File Execution Location Anomaly | Florian Roth, Patrick Bareiss, Anton Kutepov, oscd.community | Sigma Integrated Rule Set (GitHub) | 1386967 | 622 |
| Nibiru detection (Registry event and CommandLine parameters) | Ariel Millahuel | SOC Prime Threat Detection Marketplace | 1147667 | 54640 |
| File deletion via CMD (via cmdline) | Ariel Millahuel | SOC Prime Threat Detection Marketplace | 923890 | 9083 |
| Suspicious Svchost Process | Florian Roth | Sigma Integrated Rule Set (GitHub) | 845991 | 133 |
| Windows PowerShell Web Request | James Pemberton / @4A616D6573 | Sigma Integrated Rule Set (GitHub) | 805020 | 104 |
| Execution from Suspicious Folder | Florian Roth | Sigma Integrated Rule Set (GitHub) | 643979 | 5419 |
| Suspect Svchost Activity | David Burkett | Sigma Integrated Rule Set (GitHub) | 568031 | 87 |
| Direct Autorun Keys Modification | Victor Sergeev, Daniil Yugoslavskiy, oscd.community | Sigma Integrated Rule Set (GitHub) | 549037 | 130 |
| CSRSS.exe spawned from unusual location (possible mimicking) (via cmdline) | SOC Prime Team | SOC Prime Threat Detection Marketplace | 531710 | 11 |
| Swisyn Trojan (Sysmon detection) | Ariel Millahuel | SOC Prime Threat Detection Marketplace | 494316 | 108 |
| Suspicious Program Location with Network Connections | Florian Roth | Sigma Integrated Rule Set (GitHub) | 482076 | 5335 |
| Scheduled Task Creation | Florian Roth | Sigma Integrated Rule Set (GitHub) | 431585 | 473 |
| Startup Folder File Write | Roberto Rodriguez (Cyb3rWard0g), OTR (Open Threat Research) | Sigma Integrated Rule Set (GitHub) | 323029 | 118 |
| Executables Started in Suspicious Folder | Florian Roth | Sigma Integrated Rule Set (GitHub) | 318156 | 2408 |
| Suspicious Program Location Process Starts | Florian Roth | Sigma Integrated Rule Set (GitHub) | 315071 | 2406 |
| Execution File Type Other Than .exe | Max Altgelt | Sigma Integrated Rule Set (GitHub) | 314199 | 3369 |
| Possible Applocker Bypass | juju4 | Sigma Integrated Rule Set (GitHub) | 264915 | 225 |
| Author | – |
| Language | English |
| No. of Pages | 156 |
| PDF Size | 5 MB |
| Category | Education |
| Source/Credits | virustotal.com |
Sigma Rules List with Examples Book PDF Free Download